
The number of applications being hosted on cloud is increasing rapidly every day and along with it the growing risk of getting attacked and losing sensitive information.
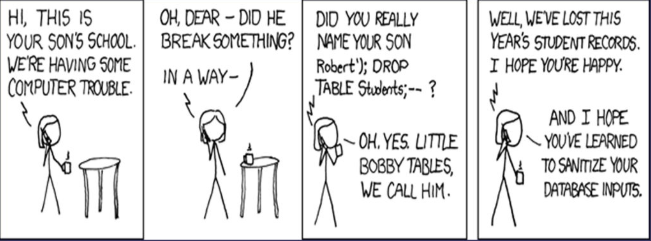
Credit: XKCD: Exploits of a Mom, published by permission.
Next comes the interesting question; who is responsible for protecting corporate data is it the service provider or the consumer?
If you are thinking it is service provider, then you would be mistaken. It is consumer’s responsibility and the service providers help us with all the necessary tools and means to ensure the web applications are guarded against such security exploits.
Threat 1: Injection
What is it?
It is one of the popular methods where a hacker gets access to the database of an application. A successful exploit allows opportunities to view, modify or even delete data. The attacker provides input data that has been crafted specifically to trick the SQL interpreter to execute commands and get access to the database.
If you are thinking you may not be impacted, then think again….
A hacker will be able to use this exploit if your application captures a user input, it can be any kind of input example:
- Registration form
- Feedback form
- Contact Us form
- Search field
Can I prevent this using a Firewall or Anti-Virus Software or something?
The fire walls like gate keepers they allow user traffic, or they block them. Firewalls do not examine every interaction and are not for detecting any malicious commands sneaked in as user inputs.
Anti-Virus software are effective in identifying malware and virus but does not have the ability to detect Injection exploits
How do I know if I am vulnerable for Injection attacks?
Any application is vulnerable if
- The data entered by users are not validated or sanitized by the application before processing it.
- The usage of non-parameterized calls or Dynamic Queries
- If your queries or stored procedures concatenates queries and data.
How do I safeguard my data from Injection attacks?
You can follow the best practices of software development such as
- Use parameterized stored procedures for constructing all your queries. They compiled before user input is processed hence the chances of modifying the actual SQL statement is prevented.
- Ensure the account that is used for connections has least privilege. Why provide read write access when the business functionality is to only read!
- Error Handling:
- If not done properly it’s like handing out the information on a platter to a hacker. Un caught SQL errors normally has lot of information such as table names and the procedure names that can be used to exploit the database.
- Validate the user input with whitelist input validation
AWS WAF has built-in capabilities to match and mitigate SQL injection attacks. You can use SQL injection match condition to deploy rules to mitigate such attacks.
The following table provides some common condition configurations
Newt Global’ s Security Vulnerability Analysis engineering teams have successfully performed Security testing for numerous applications hosted on Cloud for our numerous clients. Get in touch with us if you are looking to analyse the exposure level of your applications and to take necessary steps in preventing such attacks of your business-critical applications on cloud and we will be glad to do a free assessment for you.
ABOUT THE AUTHOR

NARASIMHA RAJU SCV – DIRECTOR
Testing Practice – Newt Global
